Related Keywords
y z data or if a graph downloadsz data or if a downloads
data visualisation graph downloads
or by frame or by chapter downloads
if the last red downloads
if the effects are not downloads
if there is a path downloads
if function downloads
if script downloads
if perl downloads
if analysis downloads
if thenrules downloads
if player downloads
if folder exists downloads
if it s not there downloads
if it contains downloads
graph downloads
graph software downloads
graph equation downloads
graph and chart downloads
Top Software Keywords
decrypt downloadsencryption downloads
aes downloads
safe downloads
encryption software downloads
decryption downloads
file encryption downloads
privacy downloads
data encryption downloads
folder lock downloads
secure downloads
password downloads
security downloads
recovery downloads
files downloads
encrypt downloads
protection downloads
file downloads
email downloads
folder downloads
protect downloads
crack downloads
hide downloads
blowfish downloads
folders downloads
lock downloads
lock folder downloads
recover downloads
rijndael downloads
des downloads
Vista Download
Vista downloadVista antivirus download
Vista wallpaper download
Vista wallpapers download
Vista themes download
Vista pack download
Vista ultimate download
Vista home download
Vista basic download
Vista business download
Vista x64 download
Vista transformation download
Vista transformation pack download
Vista boot download
Vista dvd download
Vista sidebar download
Vista aero download
Vista product key download
Top Downloads
Top Rated
Navigation: Home
\ Security & Privacy
\ Encryption Tools \ TrueCrypt
TrueCrypt7.2 by TrueCrypt Foundation |

|
Software Description:
... is a software designed to protect your important data by encrypting it. It can also maintain an on-the-fly-encrypted volume (data storage device). Files can be copied to and from a mounted TrueCrypt volume just like they are copied to/from any normal disk (for example, by simple drag-and-drop operations). ...
type: Freeware
Download TrueCryptcategories: disk encryptor, virtual disk creator, data encryptor, encryptor, decryptor, encrypt Add to Download Basket Report virus or spyware |
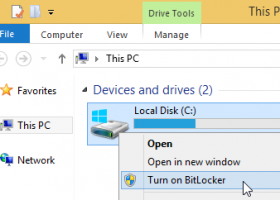 [ Zoom screenshot ] |
|
| Software Info | |
|
Best Vista Download periodically updates pricing and software information of TrueCrypt full version from the publisher,
but some information may be out-of-date. You should confirm all information. Software piracy is theft, using crack, warez passwords, patches, serial numbers, registration codes, key generator, keymaker or keygen for TrueCrypt license key is illegal and prevent future development of TrueCrypt. Download links are directly from our mirrors or publisher's website, TrueCrypt torrent files or shared files from rapidshare, yousendit or megaupload are not allowed! |
|
| Released: | May 31, 2014 |
| Filesize: | 2.60 MB |
| Platform: | Windows XP, Windows Vista, Windows Vista x64, Windows 7, Windows 7 x64, Windows 8, Windows 8 x64, Windows 10, Windows 10 x64 |
| Install | Instal And Uninstall |
| Add Your Review or Windows Vista Compatibility Report |
TrueCrypt- Releases History |
| Software: | TrueCrypt 7.2 |
| Date Released: | May 31, 2014 |
| Status: | New Release |
| Software: | TrueCrypt 7.1a |
| Date Released: | Jul 26, 2010 |
| Status: | New Release |
| Release Notes: | New features: Full compatibility with 64-bit and 32-bit Mac OS X 10.7 Lion |
| Software: | TrueCrypt 7.0 |
| Date Released: | Jul 26, 2010 |
| Status: | New Release |
| Release Notes: | · Hardware-accelerated AES (for more information, see the chapter Hardware Acceleration). Note: If you want to disable hardware acceleration, select Settings > Performance and disable the option 'Accelerate AES encryption/decryption by using the AES instructions of the processor'. · A volume can now be configured to be automatically mounted whenever its host device gets connected to the computer (provided that the correct password and/or keyfiles are supplied). Note: For example, if you have a TrueCrypt container on a USB flash drive and you want to configure TrueCrypt to mount it automatically whenever you insert the USB flash drive into the USB port, follow these steps: 1. Mount the volume. 2. Right-click the mounted volume in the drive list in the main TrueCrypt window and select 'Add to Favorites'. 3. The Favorites Organizer window should appear. |
Most popular y z data or if a graph in Encryption Tools downloads for Vista |
|
CyberSafe Files Encryption 2.1.5.1 download by CyberSoft
... software provides everything you need for keeping your data safe whether it is being sent out over ... file encryption tools provide three automatic modes of data protection. The highest level provides 448-bit BlowFish encryption ...
type: Shareware ($29.00)
View Details
Download
categories: file encryption tools, files encryption software, file encryption software, file encryption, encryption software, encryption tools, encryption |
 |
|
DiskEncryptor 1.8 download by KernSafe Technology
... allow you to read and write the right data on the disk partition until the disk is ... the following three ways to protect your personal data: Encrypt system whole disk or partition directly. Create ...
type: Freeware
View Details
Download
categories: encryption, disk encryption, cd encrypt, cd password, cd protect, disk encrypt, virtual disk, emulator |
 |
|
Protected Storage viewer 2.8 download by Scalabium Software
... recovery the sign-up passwords You may save the data as CSV/text file. ...
type: Shareware ($15.00)
View Details
Download
categories: Protected Storage, AutoComplete, password, stored, recover, reveal, crack, login, logon, password recovery, show password, show hidden password, view hidden password, password show, hidden password, see hidden passwords, showpassword, password, hidden, show, asterisk, showpw, showpassword |
 |
|
Lavasoft File Shredder 2009 7.7.0.2 download by Lavasoft AB
... in a paper shredder to protect yourself against data and identity theft. The same is true for data on your PC. Information you erase by formatting ... by Windows Vista * Clean out old, deleted data * Shred all temporary files left behind on ...
type: Trialware ($29.95)
View Details
Download
categories: flie shredder, delete file, shred file, shredder, shred, delete |
 |
|
DICOM Anonymizer&Masker 1.11 download by DICOM Tool
... and so on. DICOM Anonymizer&Maker can: -Anonymize any Data Element: user can define a list of elements ... Modality=CT, Rows=512 etc.). It can even anonymize pixel data/overlays embedded in a sequence element. -Anonymize Jpeg/RLE compressed ...
type: Commercial ($38.00)
View Details
Download
categories: DICOM Anonymizer, DICOM, DICOM Anonymizer Light, DVTk, DICOManonymizer, DICOMdumper, MIRC, DICOM Randomizer, DICOM Rewriter, MIView, CTP, Santesoft, RUBY DICOM, OFFIS, Escape Medical Viewer, OsiriX, NeoLogica, Madena, DCM4CHE, DICOM Editor, Algom |
 |
|
DirCryptHide 1.58 download by Gunnar Daehling
... will mount as another drive. When moving the data is first copied, while no error occurs, the ... deleted, at the direction of the container, the data can be shredded with the ERASER program. With ...
type: Freeware
View Details
Download
categories: Encryption, truecrypt, on the fly, hide folder, safe, tresor, container, hide, ordner, password, invisible, protect |
|
Hash Generator 8.0 download by SecurityXploded
... storage of password as well as other sensitive data to protect it from the spying eyes. HashGenerator helps in quickly computing or verifying the hash for any such file or ...
type: Freeware
View Details
Download
categories: hash generator, hash tool, hash creator, md5, sha256, md4, md2, sha512, sha1, haval, whirlpool hash, base64, crc32, alder32, rot13 |
 |
|
BestCrypt Traveller 1.06 download by Jetico Inc
... place in the world and access their encrypted data. A single BestCrypt Traveller executable can also be ... disk together with encrypted containers to access the data on any computer that might be temporarily available ...
type: Freeware
View Details
Download
categories: encryption software, BestCrypt encryption, access container file, BestCrypt, encryption, container |
 |
|
Hash Codes 1.62.780.7200 download by Marek Sienczak
... use application designed to enable users to hash data from keyboard, file or CD/DVD. This tool supports: ... RIPEMD-320 or Whirlpool algorithm. Features: Hash data from keyboard, file or CD/DVD Uses Adler32, CRC32, ...
View Details
Download
|
 |
|
Hash Codes x64 1.62.780.7200 download by Marek Sienczak
... use application designed to enable users to hash data from keyboard, file or CD/DVD. This tool supports: ... RIPEMD-320 or Whirlpool algorithm. Features: Hash data from keyboard, file or CD/DVD Uses Adler32, CRC32, ...
type: Open Source
View Details
Download
categories: x64 hash data, x64 encrypt data, x64 data encryption, x64 hash, x64 encrypt, x64 encryption |
 |